Hello Friends,
Welcome To Notebility!
This article help you to understand Clickjacking, here we will discuss like what is clickjacking, clickjacking prevention, clickjacking attack, and at the end how to prevent clickjacking, and how to test clickjacking.
Let’s start today topic What is Clickjacking Vulnerability & Clickjacking attack prevention
What is Clickjacking Vulnerability?
“Clickjacking” is a subset of the “UI redressing”. Clickjacking is a malicious technique that consists of deceiving a web user into interacting on something different from what the user believes he is interacting on.
A clickjacking attack is done in most cases by clicking on a webpage element.
Clickjacking is an attack that tricks a user into clicking a webpage element that is invisible or disguised as another element.
Clickjacking refers to any attack where the user unintentionally clicks an unexpected web page element.
You can say that whatever we show on a webpage in reality before that there is another page on the web where the page is transparent on top of a visible one page.
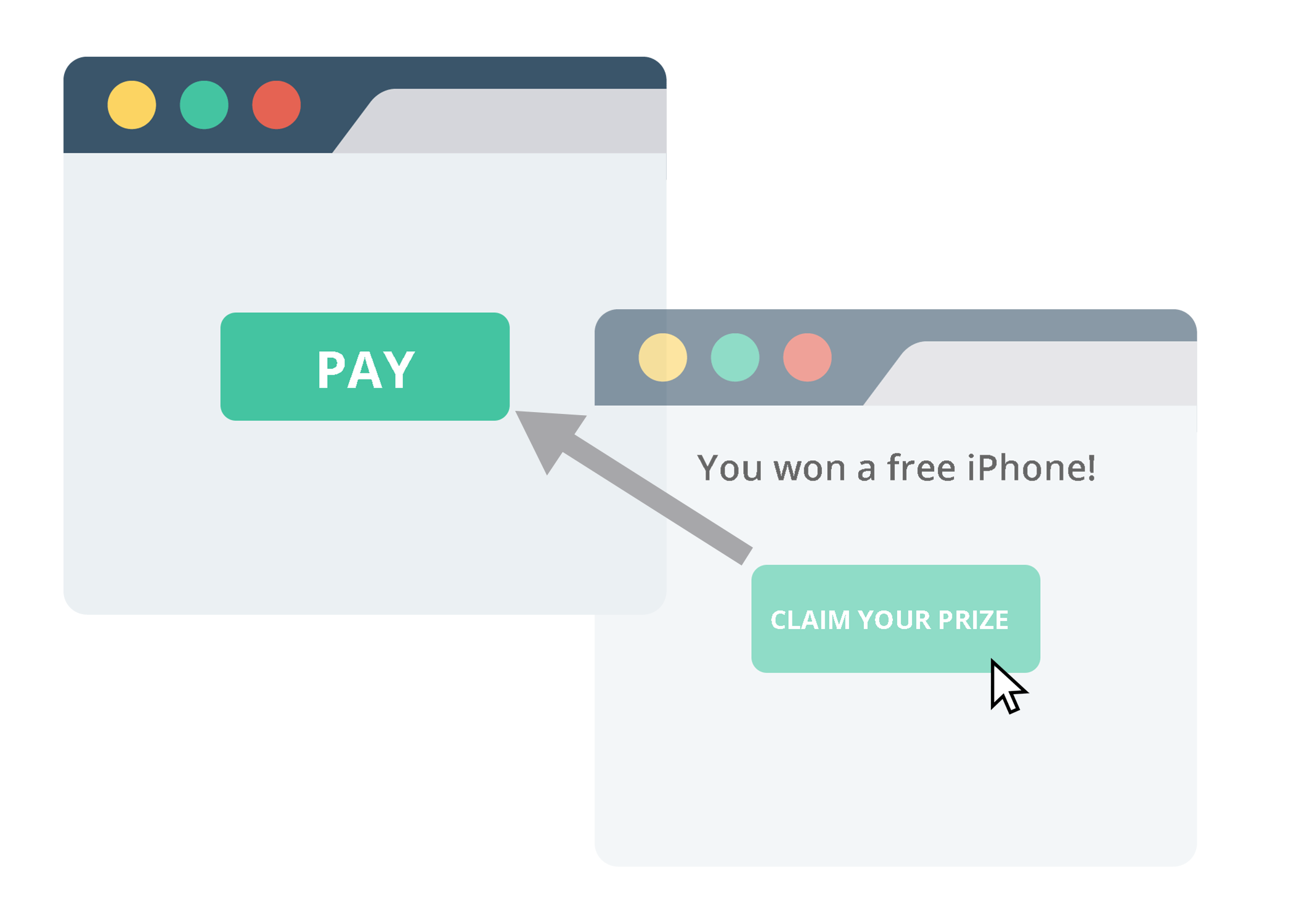
The name was coined from click hijacking, and the technique is most often applied to web pages by overlaying malicious content over a trusted page or by placing a transparent page on top of a visible one.
This type of attack, which can be used alone or in combination with other attacks, could potentially send unauthorized commands or reveal confidential information while the victim is interacting on seemingly harmless web pages.
What is the impact on the user or website?
A Clickjacking attack uses seemingly innocuous features of HTML and JavaScript to force the victim to perform undesired actions, such as clicking on a button that appears to perform another operation.
This is a “client-side” security issue that affects a variety of browsers and platforms. To carry out this type of technique the attacker has to create a seemingly harmless web the page that loads the target application through the use of an Iframe (suitably concealed through the use of CSS code).
Once this is done, the attacker could induce the victim to interact with his fictitious web page by other means (like for example social engineering).
How to prevent Clickjacking Attack?
There are two ways to protect from Clickjacking Attack :
1.Client side protection 2.Server side protection ( X-Frame-Options )
Client-side protection
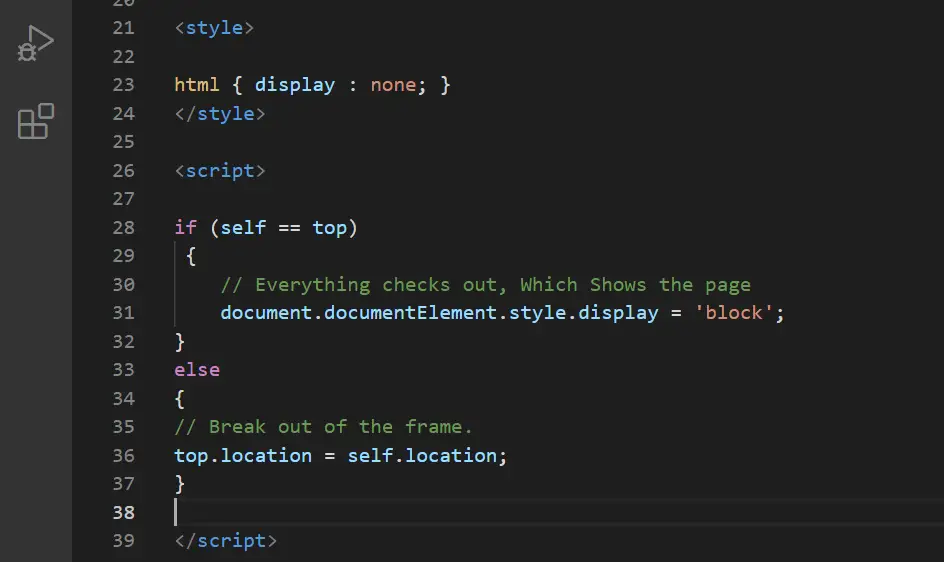
1.Frame Busting
The most common client-side method, that has been developed to protect a web page from Clickjacking, is called Frame Busting and it consists of a script on each page that should not be framed.
The aim of this technique is to prevent a site from functioning when it is loaded inside a frame.
In this technique, JavaScript that runs on the user’s browser is used to stop itself from being embedded into the iframe and escape out of it.
When the page loads, this JS code will check if the domain of the page matches the domain of the browser window.
If it does then no problem, if it does not then it will escape out of the frame and load the site in the browser by replacing the site by trying to load it in the Iframe.
For Frame Busting simply you need to add this code in your Header of a webpage:
Server-side protection
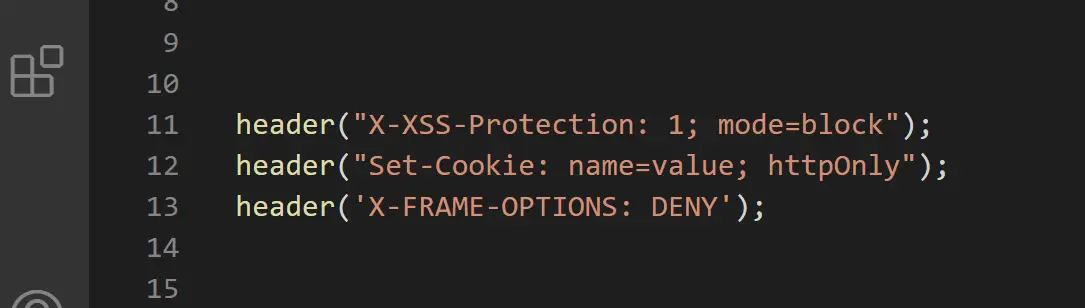
1.X-Frame-Options
An alternative approach to client-side frame busting code was implemented by Microsoft and it consists of header-based defense.
This new “X-FRAME-OPTIONS” header is sent from the the server on HTTP responses and is used to mark web pages that shouldn’t be framed.
The “X-FRAME-OPTIONS” is a very good solution, and was adopted by major browsers, but also for this technique there are some limitations that could lead in any case to exploit the clickjacking vulnerability.
X-Frame-Options is a response header. Developers can use it to protect their site against clickjacking. It can be used to indicate whether or not a browser should be allowed to render a page in an Iframe by having its value set as any of the following:
X-FRAME-OPTIONS: DENY By specifying DENY, no site will be allowed to load the page in a frame.
X-FRAME-OPTIONS: SAMEORIGIN On the other hand, if you specify SAMEORIGIN, you can still use the page in a frame as long as the site including it in a frame is the same as the one serving the page.
X-FRAME-OPTIONS: ALLOW-FROM URI If you specify this, then the site can be displayed in a frame only by URI specified. However, this is an obsolete directive that no longer works in modern browsers.
For the X-FRAME-OPTIONS simply you need to add this code in your Header of the webpage:
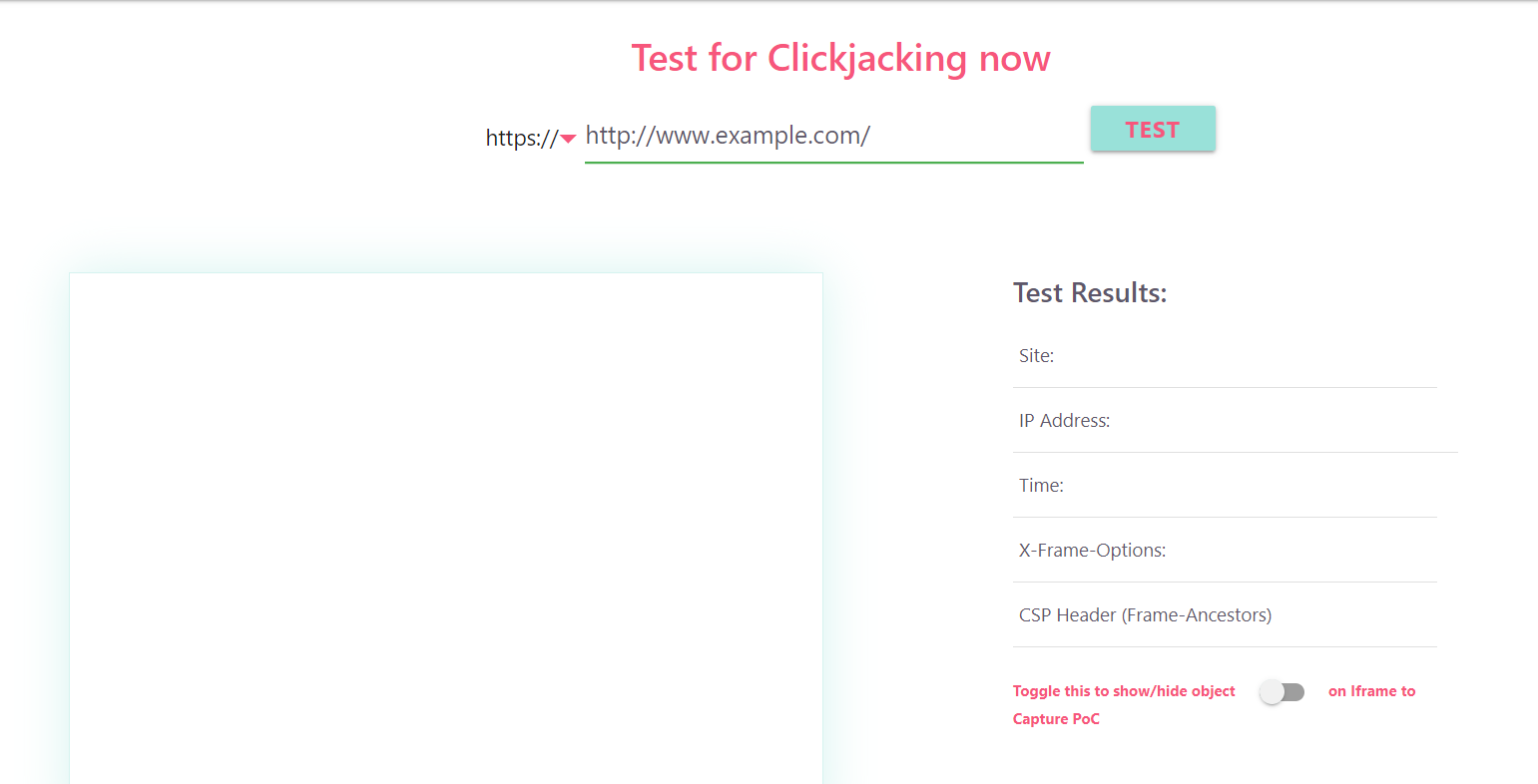
How to Test Our website is secure from Clickjacking Attacks?
There is a different way to know that your website or web-page is Vulnerable to clickjacking attacks or not.
There you can test out the whole website from a security company that can test the whole website.
But there is another way to know that your site is vulnerable to clickjacking attacks.
This website is testing your whole website and then it gives you the full report. Simply visit the clickjacker.io and put your website URL. And it will test your website frame busting and X-frame-option both which means it will test the site from the client and server-side.
Thanks for reading…